A REVIEW AND COMPARATIVE ANALYSIS OF ENCRYPTION TECHNIQUEs
Abstract
Author(s): Suchita Kumari, Akhilesh Bansiya
Due to the rapid growth of digital communication and multimedia application, security becomes an important issue of communication and storage of images. Cryptographic algorithms play a vital role in providing the data security against malicious attacks. One of the most common public key algorithms in use for secure transaction is the RSA. Hence the goal to design an efficient architecture for RSA becomes more relevant. For high secure application they need to develop new algorithm to compute such mathematical operations which are involved in cryptographic algorithm. The following paper explores the history of RSA and the method. Keywords: Cryptographic, Encryption Techniques, secure transaction

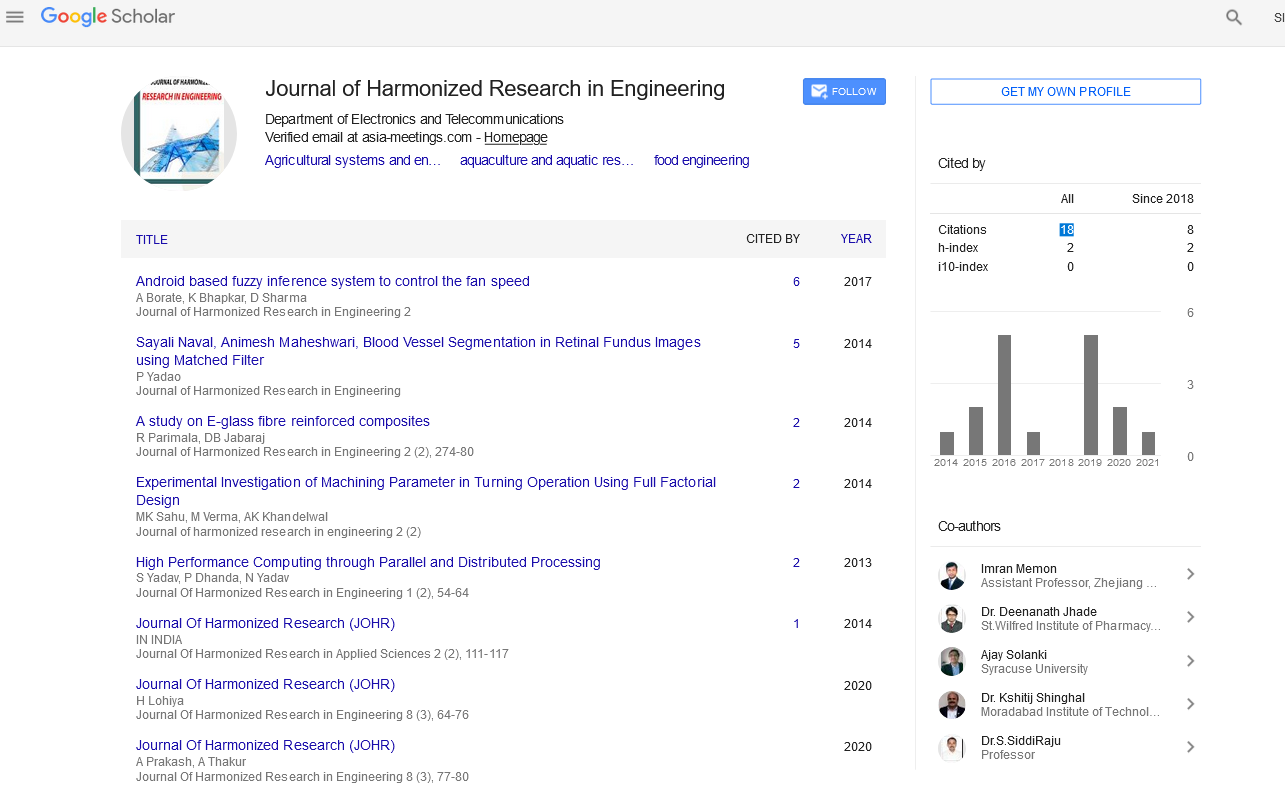
Google Scholar citation report
Citations : 43
Journal of Harmonized Research in Engineering received 43 citations as per google scholar report