SECURITY IN JAVA
Abstract
Author(s): Nisha Yadav, Shikha Yadav, Preeti Dhanda
The Java programming language collectively with its runtime environment is well known to provide a lot of security features for applications written in Java and headed for the environment, in which Java applications are deployed. Certainly, under the frequently used slogan "Java Security", quite unusual aspects regarding the security of Java applications are addressed. Java has been designed to be an intrinsic safe programming language. In particular Java does not permit to directly access or control memory. While not being element of the innermost security features, "Java Security" also encompasses some standard libraries and extensions that are shipped with SUN’s Java Development Kits (JDKs) and that are predominantly intended for the usage in security critical tasks. While the Java standard API does only classify appropriate interfaces for most of these purposes, the JDKs also embrace implementations of cryptographic and security providers. The runtime environments provided by application-level virtual machines, for instance, the Java Virtual Machine are attractive for Internet application providers because the applications can be deployed on any platform that supports the target virtual machine. By means of Internet applications, organizations in addition to end users face the threat of viruses, trojans, and denial of service attacks. Virtual machine providers are responsive of these Internet security risks and thus provide, for example, runtime monitoring of untrusted code and access control to susceptible resources.

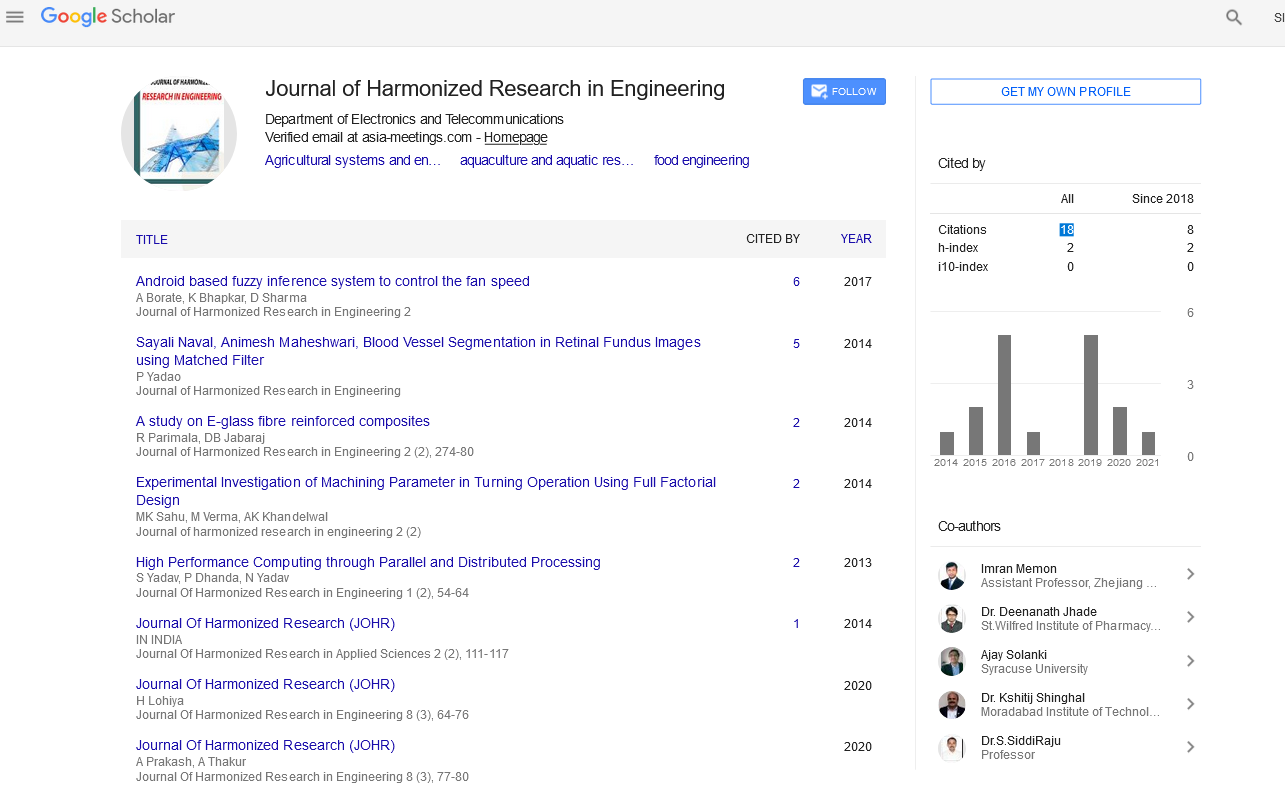
Google Scholar citation report
Citations : 43
Journal of Harmonized Research in Engineering received 43 citations as per google scholar report